August 29: The British Computer Misuse Act Goes into Effect | This Day in History | Computer History Museum
3.8 Ethical, Legal and Environmental impacts of Digital Technology on Wider Society, including issues of Privacy

Webinar: Assessing Your Risk and Preparing for the European General Data Protection Regulation (GDPR)
National Crime Agency (NCA) on Twitter: "Did you know young people may unknowingly get themselves involved in cyber crime, or be targeted by criminals wanting to use their skills? Here are some

Introduction to cyber security: stay safe online: Introduction to cyber security: 2.3 - OpenLearn - Open University

computer misuse act 1990 clipart Act of Parliament Computer Misuse Act 1990 Data Protection Act 1998 clipart - Shield, transparent clip art
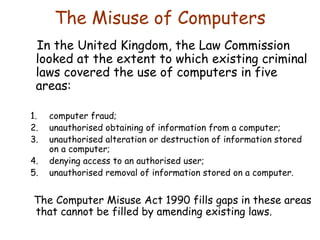
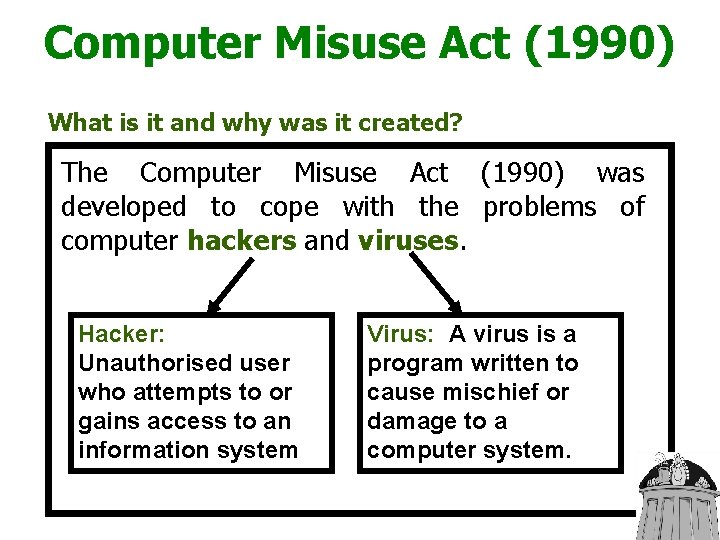
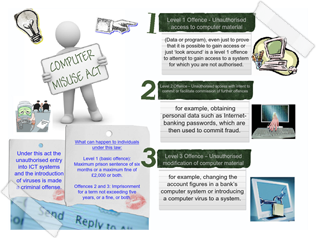
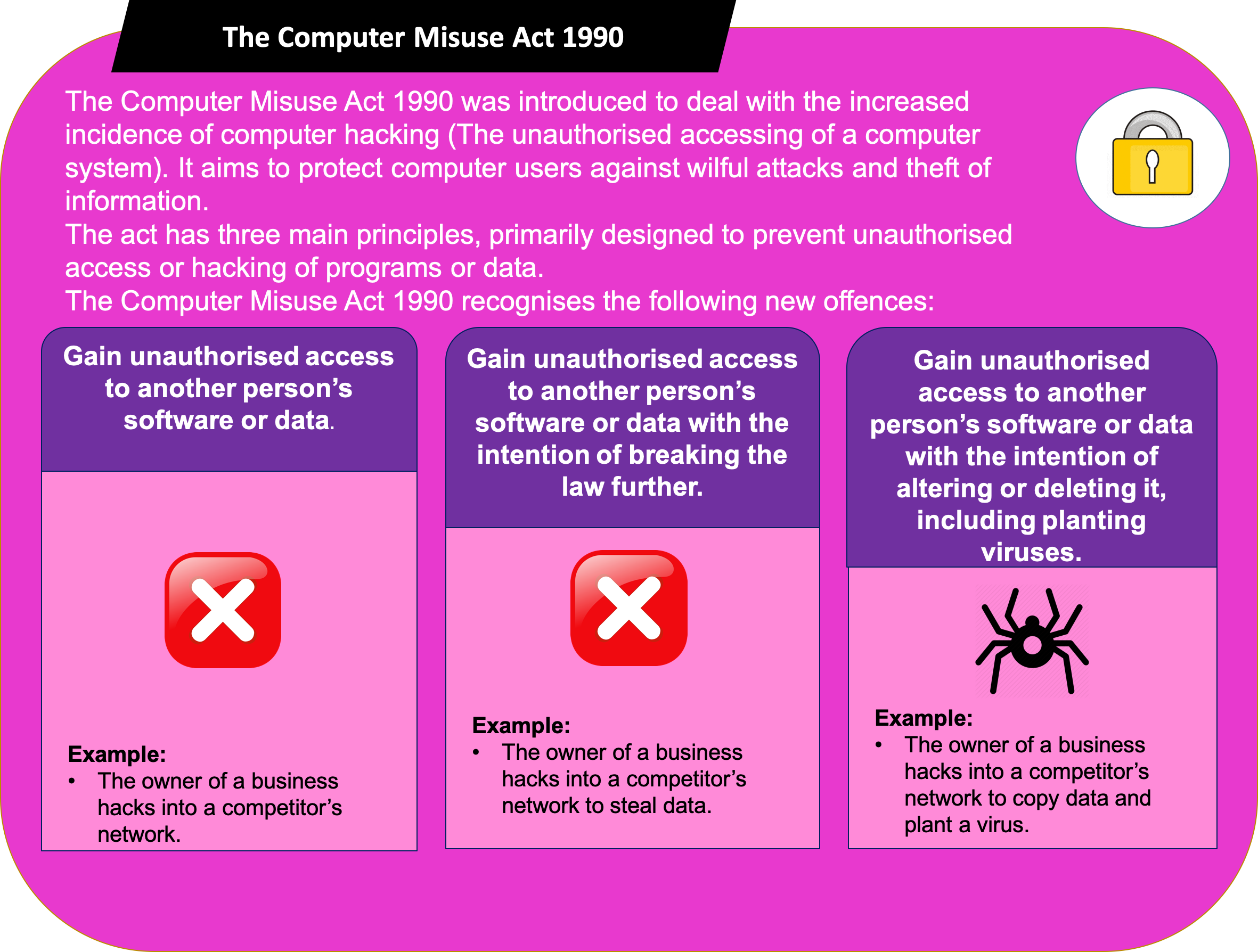
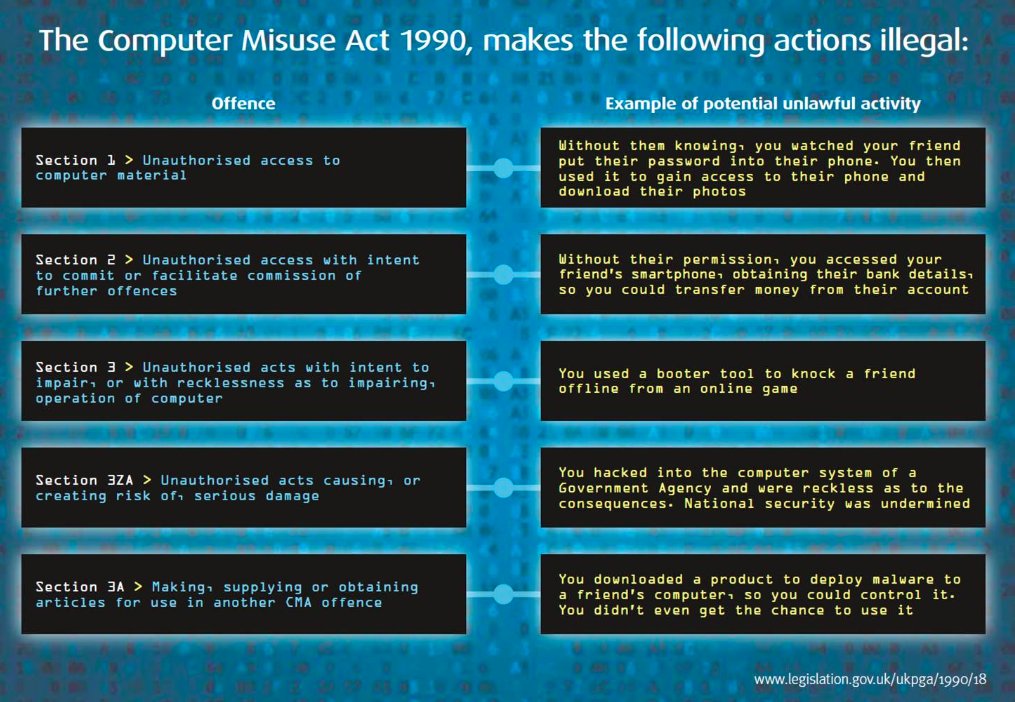
IT and the LAW. The Computer Misuse Act of 1990 In the early 1980s in the UK, hacking was not illegal. Some universities stipulated that hacking, especially. - ppt download